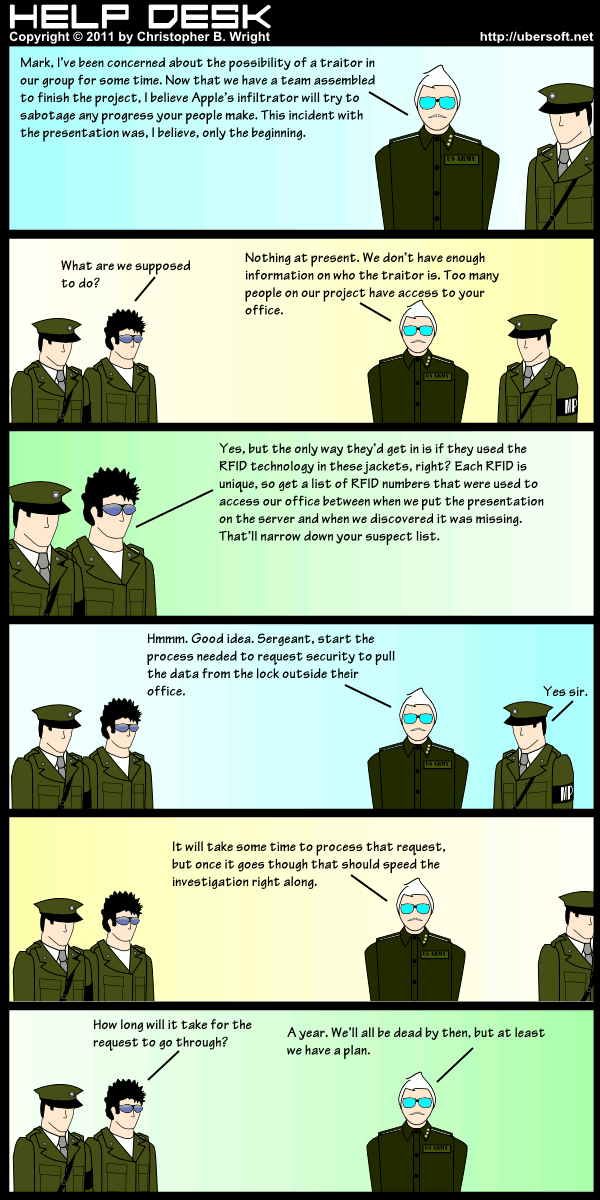
Comic Transcript
GENERAL RICHMOND MONTGOMERY: Mark, I’ve been concerned about the possibility of a traitor in our group for some time. Now that we have a team assembled to finish the project, I believe Apple’s infiltrator will try to sabotage any progress your people make. This incident with the presentation was, I believe, only the beginning.
MARK: What are we supposed to do?
GENERAL RICHMOND MONTGOMERY: Nothing at present. We don’t have enough information on whot he traitor is. Too many people on our project have access to your office.
MARK: Yes, but he only way they’d get in is if they used the RFID technology in these jackets, right? Each RFID is unique, so get a list of RFID numbers that were used to access our office between when we put the presentation on the server and when we discovered it was missing. That’ll narrow down your suspect list.
GENERAL RICHMOND MONTGOMERY: Hmmm. Good idea. Sergeant, start the process needed to request security to pull the data from the lock outside their office.
MILITARY POLICEMAN: Yes sir.
GENERAL RICHMOND MONTGOMERY: It will take some time to process that request, but once it goes through that should sped the investigation right along.
MARK: How long will it take for the request to go through?
GENERAL RICHMOND MONTGOMERY: A year. We’ll all be dead by then, but at least we have a plan.